Hi everyone, I think it is best to reveal more information about this technology.
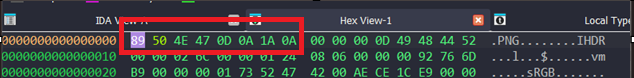
As for the source, it’s a radionics project called infopathy. The record the EM signal of substances, and play them to water for the substance’s effect. You can search for it online. They, not me, discovered that when doing some sort of job on 2 files closer together, you can create a link between them. When you use the way above - you can influence a person and the target.
They are using it through these wav files, but I found that you can connect pretty much anything you can represent. I’ve already used their em files it to disrupt an adversaries hardware in a key moment, but I can’t divulge exactly what I did, nor will you believe me.
In any case, I have hit a roadblock. Although this technique can connect files (and place, and people and events…) to people and the like, I can’t seem to figure out how to use it for manifesting, or in other words, magick. I have more success conducting magick myself then using this technique, which is a big shame, because the potential I believe is great.
A word of caution – you shouldn’t run any version of this technology on your own PC for long periods, unless you discover a way of protecting your self from the EM waves. You will be exposed to the essence of the person you are influencing, and in close distance, and it can hurt you. However, for testing purposes, I don’t see why not.
I am working on recording the EM signal of orgone, but I believe a photo of an orgone generator might be just as good. Still, it doesn’t help manifestation, so recording orgone is my next step in this research.
I would also note that the infopathy substance files are not being played (in this technique), just hashed. But the connection between an audio file description and its state in the world is so great, the link appears to be extremely effective.
I consider my approach, although revolutionary, primitive – and this is why I am revealing to you my research this past half-year. My hope is that together, we can discover a free way to conduct radionics operations without the need of electrical equipment, while keeping the benefits that this equipment provides.
I can say more, I can probably write a quarter book on this already, but the best way to find out… is for yourselves.